Microsoft 365 Defender Services
- Sanjay Kumar

- Dec 4, 2020
- 5 min read
To say that Microsoft's security services naming is puzzling is an understatement. This article will alleviate the confusion and cover each of the different products and services, which area they provide value for, and how they fit together under the larger Microsoft Threat Protection umbrella.
Microsoft Defender for Identity
Microsoft Defender for Identity (a much more descriptive name, the old name was confusing as it has very little to do with Azure) is a cloud solution that's somewhat unique in this line-up, as it's mostly focused on your on-premises Active Directory (AD). When an attacker gains a foothold in your corporate network, they'll perform different actions such as lateral movement (compromising more machines) to eventually be able to elevate privileges to server or domain administrator, leading to domain dominance. These activities leave a trail on your domain controllers (DCs). Microsoft Defender for Identity is specifically designed to identify and catch them.
To get started with Microsoft Defender for Identity, you first create your instance in the cloud, and then you install the sensors on all your DCs. In very high security environments, you can use a standalone sensor on a member server with event forwarding. The sensor monitors the event log and captures the relevant network packets. Microsoft Defender for Identity uses machine learning to build an understanding of what's normal behavior for both user accounts and devices/network endpoints in your networks.
Microsoft Defender for Office 365
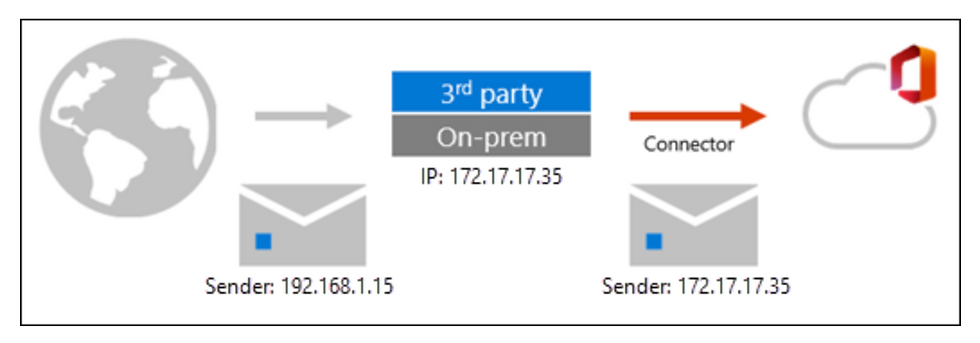
Microsoft Defender for Office 365 builds on top of Exchange Online Protection (EOP) that all users of Exchange in the cloud are protected by. EOP provides connection, spam, and malware filtering settings for incoming email, outbound spam settings, and quarantine of questionable emails and Domain Keys Identified Mail (DKIM) settings.
If these policies don't catch enough bad stuff, you can enable Microsoft Defender for Office 365 policies. These include Safe Attachments, which will open unknown email attachments in a VM and identify whether they're malicious. Safe Links does the same for URLs in emails (at the time of click) and both are available across SharePoint, OneDrive, Microsoft Teams, and Exchange Online. Microsoft Defender for Office 365 Protection Plan 2 adds features such as Threat Trackers, Threat Explorer, automated investigation and response, and Attack Simulator for testing your defenses.
Microsoft Defender for Office 365 comes in two flavors. Plan 1 comes with Microsoft 365 Business Premium or as an add-on, and Plan 2 comes with Microsoft 365 E5 or O365 E5, or you can buy either P1 or P2 as standalone licenses.
Microsoft Defender for Endpoint
Microsoft Defender for Endpoint is a full-fledged endpoint detection and response (EDR) tool for Windows, Linux, MacOS, and Android, with iOS in preview. On Windows, it builds on top of Windows Defender. This means deploying Microsoft Defender for Endpoint isn't about deploying an agent but simply about onboarding the endpoint into Microsoft Defender for Endpoint to unlock the advanced features. You can onboard a few test devices by running a local script, but for larger volumes, you'll want to use Microsoft Endpoint Manager Configuration Manager (SCCM) or Microsoft Endpoint Manager (Intune).
Microsoft Defender for Endpoint uses machine learning models, some running locally and some in the cloud to protect each endpoint against threats. It's also a full EDR solution, so it inventories all software that's installed on each device and all processes that are running. At Ignite 2020 Microsoft furthered the vision of Microsoft 365 Defender by labelling the whole stack together as Extended Detection and Response (XDR), as each component works together with the others, it's not just about protecting endpoints but holistically respond to attacks across servers, applications, and your hybrid infrastructure.
Old timers reading this might remember a free tool called EMET, some of its attack surface reduction tech is in Microsoft Defender for Endpoint , along with Threat and Vulnerability Management which identifies vulnerable versions of installed software and prioritizes what needs to be patched first, and hands this over as a job to the desktop team. Automated investigation and response provide automated remediation of threats with an undo button. Finally, Microsoft Defender for Endpoint also gives you access to Microsoft Threat Experts, SOC analysts at Microsoft, providing a managed threat hunting service to complement your own security analysts.
New features revealed at Ignite include the move to System extensions from Kernel extensions for the new MacOS, the iOS agent and Defender Application Guard for Office, providing an isolated VM security boundary for untrusted Word, Excel and PowerPoint documents in a similar way to how Edge can handle untrusted web sites today.
Microsoft Defender for Endpoint is part of Windows 10 Enterprise E5, Microsoft 365 E5 or Microsoft 365 E5 Security.
Azure Defender
Azure Defender provides insight into the security posture of your IaaS and PaaS resources in Azure, including often giving you the option to "fix" issues with a single button click. Azure Defender also extends to any VM in any cloud, including on-premises with an agent. This includes Secure Score integration so that your cloud security posture in GCP and AWS is reflected in Azure Defender. With the standard version ("paid for") of Azure Defender, you get Microsoft Defender for Endpoint for servers included.
Azure Defender for SQL now extends to your servers on-premises and in other clouds and the recent acquisition of CyberX is integrated to provide protection for existing Operational Technology deployments.
Azure identity protection is part of Azure Active Directory (AAD) and uses machine learning to build up a profile of your users' sign-in behaviors. It combines these with signals from the Intelligent Security Graph to identify risks associated with each user credential.
You then build user and sign-in risk policies that can take certain actions. For example, Jane normally logs in from Australia on her corporate laptop. If her username and password are used to log in from an unknown device in India, the policy will kick in and prompt MFA (or block the login).
Microsoft Cloud App Security is a cloud access security broker, which basically means it's a firewall in the cloud, securing SaaS application access for your users. Microsoft Cloud App Security lets you discover services that your users are using (Shadow IT), unsanction ones that don't meet your corporate standards, and sanction those that do. It also lets you apply policies for documents that are uploaded to cloud storage (OneDrive, DropBox, Box, etc.), do real-time DLP in sessions, and mitigate threats.
MEM is the new name for Intune, a cloud service that provides mobile device management (MDM) and mobile application management (MAM). MEM is also the new name for System Center Configuration Manager, now positioned as the "edge computing" part of MEM.
It's also a way to simplify licensing. The most common question Microsoft received around Intune/SCCM was if I have licensing for one, can I use the other one? Well, now you can. It's a hybrid solution where all your on-premises resources are managed by SCCM but controlled from the cloud console, and your mobile assets are managed from the same console through Intune.
Together, they provide numerous security features, including the ability to distribute apps to any platform, as well as control corporate data and prohibit it from being leaked into non-business apps.
The enterprise version of Windows 10 unlocks a number of security features, such as Credential Guard for Remote Desktop, Windows Hello for Business, BitLocker, and Windows Information Protection to separate corporate and personal data.
Azure Sentinel
This cloud-based SIEM is quickly growing in popularity and integrates with several of the other services easily. A SIEM is a centralized database of event logs from all your devices, servers, networking infrastructure, etc. This is then analyzed for evidence of intrusion, raising alerts as required. Analysts use automated and manual search tools to hunt through the data to identify signals from attackers. Importantly, if you're an SMB that is using O365/M365, know that ingesting the unified audit log from there as well as alerts from the ATP services is totally free—a good reason to learn a bit about Sentinel and set up a POC.

Comments